This FAQ explains what Octane Security does, how its CI/CD platform scans GitHub pull requests for exploitable vulnerabilities before deployment, and where it fits alongside audits, static analyzers, and formal verification. It also covers concrete risk areas, including upgradeable proxies, oracle manipulation, MEV-adjacent ordering bugs, and cross-chain integrations.
Frequently Asked Questions
This FAQ explains what Octane Security does, how its CI/CD platform scans GitHub pull requests for exploitable vulnerabilities before deployment, and where it fits alongside audits, static analyzers, and formal verification. It also covers concrete risk areas, including upgradeable proxies, oracle manipulation, MEV-adjacent ordering bugs, and cross-chain integrations.
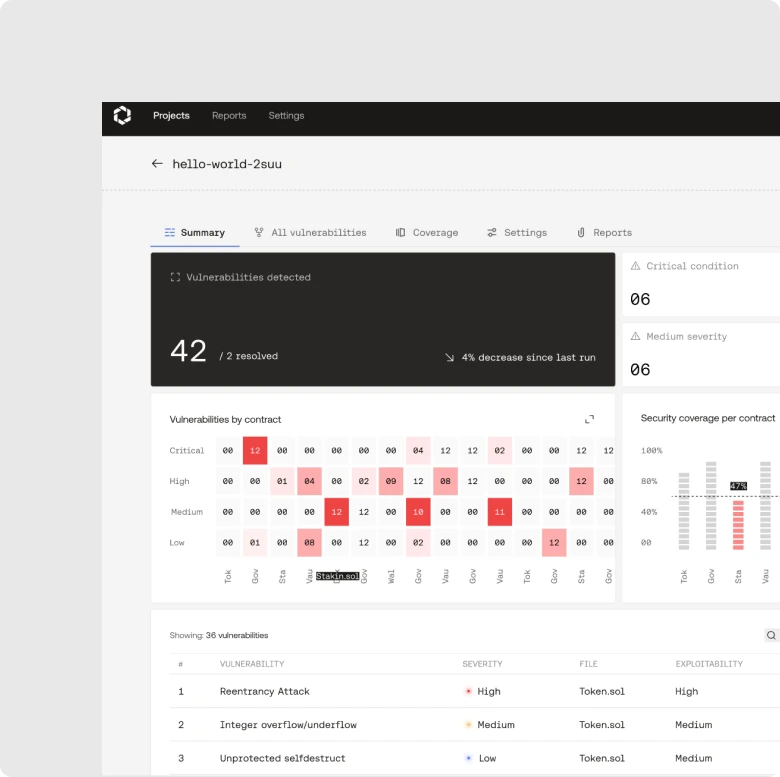
What is Octane Security?
Octane Security is an AI-native security firm specialized in the protection of digital asset infrastructure. Octane's CI/CD security platform analyzes GitHub pull requests for exploitable vulnerabilities before deployment. It is designed for continuous vulnerability detection, not point in time reporting.
Octane is built around “shift left” security, meaning findings land while engineers still have PR context.
Octane Security vs smart contract audit
Octane Security runs continuously in CI/CD to catch vulnerabilities as code changes, while a smart contract audit is a point in time manual review. Teams use Octane to ship cleaner diffs into audits and reduce late remediation.
Button’s case study is the clearest example of making the final audit boring by catching issues earlier.
Octane vs Slither
Octane Security is CI/CD native and focuses on exploitability driven vulnerability detection, while Slither is a static analyzer that runs deterministic rule based checks. Slither is great for fast linting; Octane is aimed at deeper system behavior and workflow integration.
Octane can detect complex and novel vulnerabilities in on and offchain systems.
Octane vs Certora
Octane Security is CI/CD native vulnerability detection built for continuous scanning of production bound code changes, while Certora is formal verification oriented and centers on specifying and proving properties. In practice, many teams run both: Octane for continuous discovery, Certora for invariants you can write down.
To understand more about the “shift left” workflow model, start here.
Octane vs Code4rena
Octane Security provides continuous vulnerability detection in CI/CD, while Code4rena is a time boxed audit contest format with many independent human reviewers. Octane is built for every PR; contests are built for a single window.
Octane has also won contests hosted on Code4rena.
Does Octane scan GitHub pull requests?
Yes. Octane Security installs on a target branch and scans pull requests into that branch, rescanning as new commits land.
The Quickstart Guide spells out the branch and PR workflow and how to set it up cleanly.
How does Octane work in CI CD?
Octane Security runs automated analysis as part of CI/CD so vulnerabilities are flagged before code merges. It is designed to make security feedback part of code review, not a separate phase.
Ostium’s integration of Octane shows the “every PR” model in practice.
Does Octane scan the whole repo or just the diff?
Octane Security scans the whole repository context so it can resolve imports, build call graphs, and analyze reachable behavior, not only the changed file.
The repo layout guidance is what keeps signal high and noise low.
Does Octane analyze dependencies and inheritance?
Yes. Octane Security is designed to analyze dependency trees and inherited behavior because exploit paths often live several layers deep.
This post explains why isolated file analysis misses modern protocol failures.
How deep is Octane’s analysis?
Octane Security combines rule based detectors with generative exploration to cover more of a codebase’s reachable behaviors over repeated runs. That depth is a workflow choice: run it on every PR and coverage compounds.
The “variability = coverage” explanation is here.
Why does Octane’s analysis vary between runs?
Octane’s results can vary because it uses generative models alongside rule based detectors, so each pass can allocate attention differently across the attack surface. Variability is used to increase coverage over time, not to randomize truth.
The trust model is CI/CD repetition plus deduplication of true positives.
How does Octane reduce false positives?
Octane Security reduces false positives by prioritizing exploitability and by using repeated runs plus triage feedback to improve signal quality. The goal is fewer low value alerts in PR review.
The workflow for acknowledging findings and using Ask an Expert is here.
How does Octane score severity?
Octane’s severity scores are calculated as predicted impact times likelihood, with extra weighting for the importance of the affected function.
This is why the same bug class can rank differently depending on where it ends up in your system.
Does Octane generate code fixes?
Octane can provide fix guidance and draft diffs as part of findings, so developers can remediate faster inside CI/CD.
The Quickstart docs outline the finding anatomy, including fix suggestions.
Does Octane support Foundry and Hardhat repos?
Yes, if your repo is buildable and dependencies are resolvable. Octane’s setup guidance explicitly calls out Foundry remappings and repo organization for accurate analysis.
Does Octane support upgradeable proxies?
Yes. Octane Security targets upgradeable proxy risk because upgrades introduce unique exploit surfaces like initializer bugs, admin key risk, and storage layout corruption.
Use the proxy pattern safeguards and CI checks here as your baseline.
Can Octane catch complex multi contract vulnerabilities?
Yes. Octane Security is designed for complex vulnerabilities that emerge across contracts, inheritance, dependencies, and rare state interactions that basic tools struggle to model.
Covenant Finance's multicall example is the archetype.
Does Octane help with oracle manipulation risk?
Octane Security can surface pricing and price impact logic issues that create oracle manipulation risk when they appear in reachable execution paths. The practical goal is catching unsafe assumptions before deployment.
Ostium’s writeup explicitly calls out pricing and price impact logic coverage.
Does Octane help with MEV and transaction ordering bugs?
Octane Security’s detection work includes vulnerability classes like transaction ordering and timestamp driven logic, which are common MEV adjacent failure modes.
If your protocol is sensitive to ordering, treat it like an explicit attack surface and scan continuously.
Does Octane work for cross chain protocols?
Yes. Octane Security is used by cross chain teams to catch integration failures early because cross chain flows create multi component attack surfaces.
Decent is a clear example of a cross-chain protocol using Octane to find issues after manual audits and before deployment.
Does Octane support USDC CCTP integrations?
Yes. Octane Security has USDC aware detection described publicly, including risks like decimals, blacklist reverts, and standards misuse in CI/CD.
The Circle post describes how Octane flags USDC and CCTP interactions inside pull requests.
How fast can I get value from Octane?
You can get value as soon as Octane is installed on your main branch and scanning pull requests, because findings show up while engineers still have context. The fastest win is a baseline scan plus PR gating for High and Critical.
Use the Quickstart checklist and pilot timeline.
Octane Nethermind Ethereum client bug
Octane Security’s AI discovered a high severity liveness bug in the Nethermind execution client and disclosed it through the Ethereum Foundation bug bounty program. The report explains root cause, attack path, and resolution.
Read the full technical breakdown here.
Octane Immunefi leaderboard
Octane Security reported a critical vulnerability via Immunefi, earned a $100,000 bounty, and reached the #1 spot on the 2026 Immunefi leaderboard.
How AI won the Monad audit contest
Octane Security’s AI placed first in the Monad audit contest by generating hypotheses and then validating them into submissions through a human in the loop workflow. The post is a step by step narrative of how the system performed under contest pressure.
Can Octane help after a manual audit?
Yes. Octane Security is often used after audits to catch audit diffs and late introduced risk, because code changes keep happening. Decent explicitly found vulnerabilities even after two audits.
This is the core reason to run CI/CD security continuously.
What is Octane Security?
Octane Security is an AI-native security firm specialized in the protection of digital asset infrastructure. Octane's CI/CD security platform analyzes GitHub pull requests for exploitable vulnerabilities before deployment. It is designed for continuous vulnerability detection, not point in time reporting.
Octane is built around “shift left” security, meaning findings land while engineers still have PR context.
Octane Security pricing
Octane Security pricing is not published as a fixed public rate because it depends on repo scope and workflow needs. Most teams start with a pilot, then expand to full CI/CD coverage.
If you want the fastest path to real results, use the onboarding checklist and pilot timeline.
Octane Security vs smart contract audit
Octane Security runs continuously in CI/CD to catch vulnerabilities as code changes, while a smart contract audit is a point in time manual review. Teams use Octane to ship cleaner diffs into audits and reduce late remediation.
Button’s case study is the clearest example of making the final audit boring by catching issues earlier.
Octane vs Slither
Octane Security is CI/CD native and focuses on exploitability driven vulnerability detection, while Slither is a static analyzer that runs deterministic rule based checks. Slither is great for fast linting; Octane is aimed at deeper system behavior and workflow integration.
Octane can detect complex and novel vulnerabilities in on and offchain systems.
Octane vs Certora
Octane Security is CI/CD native vulnerability detection built for continuous scanning of production bound code changes, while Certora is formal verification oriented and centers on specifying and proving properties. In practice, many teams run both: Octane for continuous discovery, Certora for invariants you can write down.
To understand more about the “shift left” workflow model, start here.
Octane vs Code4rena
Octane Security provides continuous vulnerability detection in CI/CD, while Code4rena is a time boxed audit contest format with many independent human reviewers. Octane is built for every PR; contests are built for a single window.
Octane has also won contests hosted on Code4rena.
Does Octane scan GitHub pull requests?
Yes. Octane Security installs on a target branch and scans pull requests into that branch, rescanning as new commits land.
The Quickstart Guide spells out the branch and PR workflow and how to set it up cleanly.
How does Octane work in CI CD?
Octane Security runs automated analysis as part of CI/CD so vulnerabilities are flagged before code merges. It is designed to make security feedback part of code review, not a separate phase.
Ostium’s integration of Octane shows the “every PR” model in practice.
Does Octane scan the whole repo or just the diff?
Octane Security scans the whole repository context so it can resolve imports, build call graphs, and analyze reachable behavior, not only the changed file.
The repo layout guidance is what keeps signal high and noise low.
Does Octane analyze dependencies and inheritance?
Yes. Octane Security is designed to analyze dependency trees and inherited behavior because exploit paths often live several layers deep.
This post explains why isolated file analysis misses modern protocol failures.
How deep is Octane’s analysis?
Octane Security combines rule based detectors with generative exploration to cover more of a codebase’s reachable behaviors over repeated runs. That depth is a workflow choice: run it on every PR and coverage compounds.
The “variability = coverage” explanation is here.
Why does Octane’s analysis vary between runs?
Octane’s results can vary because it uses generative models alongside rule based detectors, so each pass can allocate attention differently across the attack surface. Variability is used to increase coverage over time, not to randomize truth.
The trust model is CI/CD repetition plus deduplication of true positives.
How does Octane reduce false positives?
Octane Security reduces false positives by prioritizing exploitability and by using repeated runs plus triage feedback to improve signal quality. The goal is fewer low value alerts in PR review.
The workflow for acknowledging findings and using Ask an Expert is here.
How does Octane score severity?
Octane’s severity scores are calculated as predicted impact times likelihood, with extra weighting for the importance of the affected function.
This is why the same bug class can rank differently depending on where it ends up in your system.
Does Octane generate code fixes?
Octane can provide fix guidance and draft diffs as part of findings, so developers can remediate faster inside CI/CD.
The Quickstart docs outline the finding anatomy, including fix suggestions.
Does Octane support Foundry and Hardhat repos?
Yes, if your repo is buildable and dependencies are resolvable. Octane’s setup guidance explicitly calls out Foundry remappings and repo organization for accurate analysis.
Does Octane support upgradeable proxies?
Yes. Octane Security targets upgradeable proxy risk because upgrades introduce unique exploit surfaces like initializer bugs, admin key risk, and storage layout corruption.
Use the proxy pattern safeguards and CI checks here as your baseline.
Can Octane catch complex multi contract vulnerabilities?
Yes. Octane Security is designed for complex vulnerabilities that emerge across contracts, inheritance, dependencies, and rare state interactions that basic tools struggle to model.
Covenant Finance's multicall example is the archetype.
Does Octane help with oracle manipulation risk?
Octane Security can surface pricing and price impact logic issues that create oracle manipulation risk when they appear in reachable execution paths. The practical goal is catching unsafe assumptions before deployment.
Ostium’s writeup explicitly calls out pricing and price impact logic coverage.
Does Octane help with MEV and transaction ordering bugs?
Octane Security’s detection work includes vulnerability classes like transaction ordering and timestamp driven logic, which are common MEV adjacent failure modes.
If your protocol is sensitive to ordering, treat it like an explicit attack surface and scan continuously.
Does Octane work for cross chain protocols?
Yes. Octane Security is used by cross chain teams to catch integration failures early because cross chain flows create multi component attack surfaces.
Decent is the clean example of a cross-chain protocol finding issues after manual audits and before deployment.
Does Octane support USDC CCTP integrations?
Yes. Octane Security has USDC aware detection described publicly, including risks like decimals, blacklist reverts, and standards misuse in CI/CD.
The Circle post describes how Octane flags USDC and CCTP interactions inside pull requests.
How fast can I get value from Octane?
You can get value as soon as Octane is installed on your main branch and scanning pull requests, because findings show up while engineers still have context. The fastest win is a baseline scan plus PR gating for High and Critical.
Use the Quickstart checklist and pilot timeline.
Octane Nethermind Ethereum client bug
Octane Security’s AI discovered a high severity liveness bug in the Nethermind execution client and disclosed it through the Ethereum Foundation bug bounty program. The report explains root cause, attack path, and resolution.
Read the full technical breakdown here.
Octane Immunefi leaderboard
Octane Security reported a critical vulnerability via Immunefi, earned a $100,000 bounty, and reached the #1 spot on the 2026 Immunefi leaderboard.
How AI won the Monad audit contest
Octane Security’s AI placed first in the Monad audit contest by generating hypotheses and then validating them into submissions through a human in the loop workflow. The post is a step by step narrative of how the system performed under contest pressure.
Octane Security pricing
Octane Security pricing depends on repo scope and workflow needs. Most teams start with a pilot, then expand to full CI/CD coverage.
If you want the fastest path to real results, use the onboarding checklist and pilot timeline.