The AI Security Layer for Mission-Critical Software
Octane finds vulnerabilities missed by your manual audits and pentests.
%201.png)













%201.png)













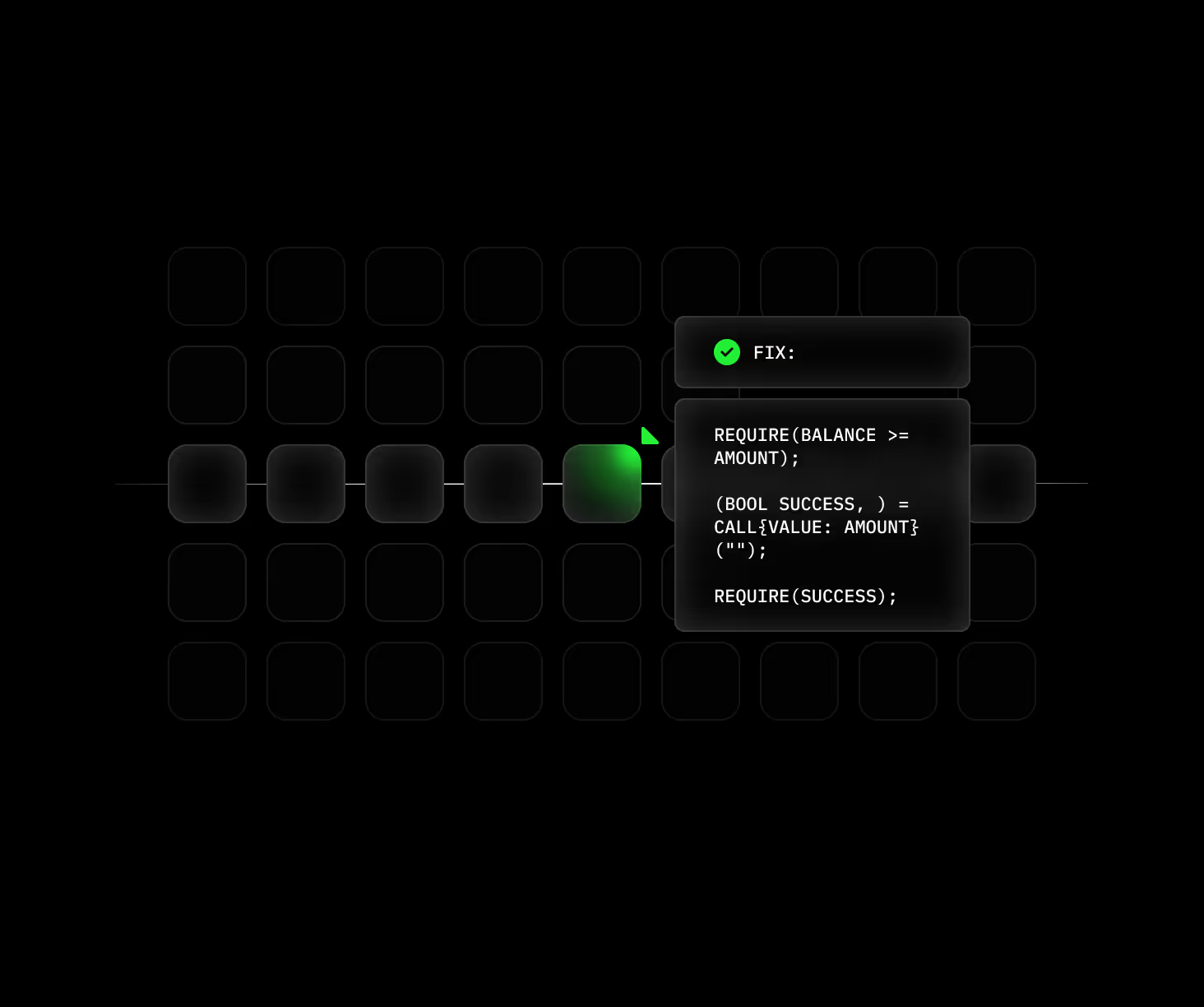
Clear Exploits, Zero Noise
Most tools flag patterns. Octane traces how your system actually behaves — following execution paths across your codebase to uncover how vulnerabilities can be exploited in practice.
Octane delivered findings equivalent to
a world-class auditor.
Our Impact
Choose your security model
Continuous Analysis
Analyze every PR in context and catch exploitable vulnerabilities before they reach production.
Baseline / On-Demand
Run a full scan before audits, launches, or major releases to identify risk across your codebase.
Adversarial Research
Work with security experts to uncover complex vulnerabilities and validate real-world exploitability.
"Octane is the first product I've seen that produces what security and development teams actually need: specific, exploitable vulnerabilities with demonstrated impact—along with the context required to fix the issues at the source. I wish I had something like this when I was building the DevSecOps program at Thermo Fisher Scientific."
Security for mission-critical systems

lorem ipsum dolor sitamet consectetur
adipiscing elit nunc pulvinar
duis uarte irureet anim sit amet
Security that keeps pace with your commits.
AI apps introduce new risks — exposed APIs, untrusted inputs, rushed auth, unaudited dependencies — while your team is buried in noisy alerts.
Octane analyzes every PR, surfaces only real vulnerabilities, and delivers the fix alongside the finding.

lorem ipsum dolor sitamet consectetur
adipiscing elit nunc pulvinar
duis uarte irureet anim sit amet
Audits satisfy regulators, but they don't stop exploits.
Octane fills that gap. Every pull request is analyzed for exploitable paths, from auth bypasses to logic flaws, with clear root cause and fix guidance. Your team gets actionable signal — and proof issues were caught before release.

lorem ipsum dolor sitamet consectetur
adipiscing elit nunc pulvinar
duis uarte irureet anim sit amet
Security starts at the foundation.
These issues aren’t obvious — they hide in dependency chains and cross-component execution paths that static tools and manual reviews miss.
Octane analyzes your full dependency graph, tracing execution across components to show where vulnerabilities originate, how they spread, and how to fix them.

lorem ipsum dolor sitamet consectetur
adipiscing elit nunc pulvinar
duis uarte irureet anim sit amet
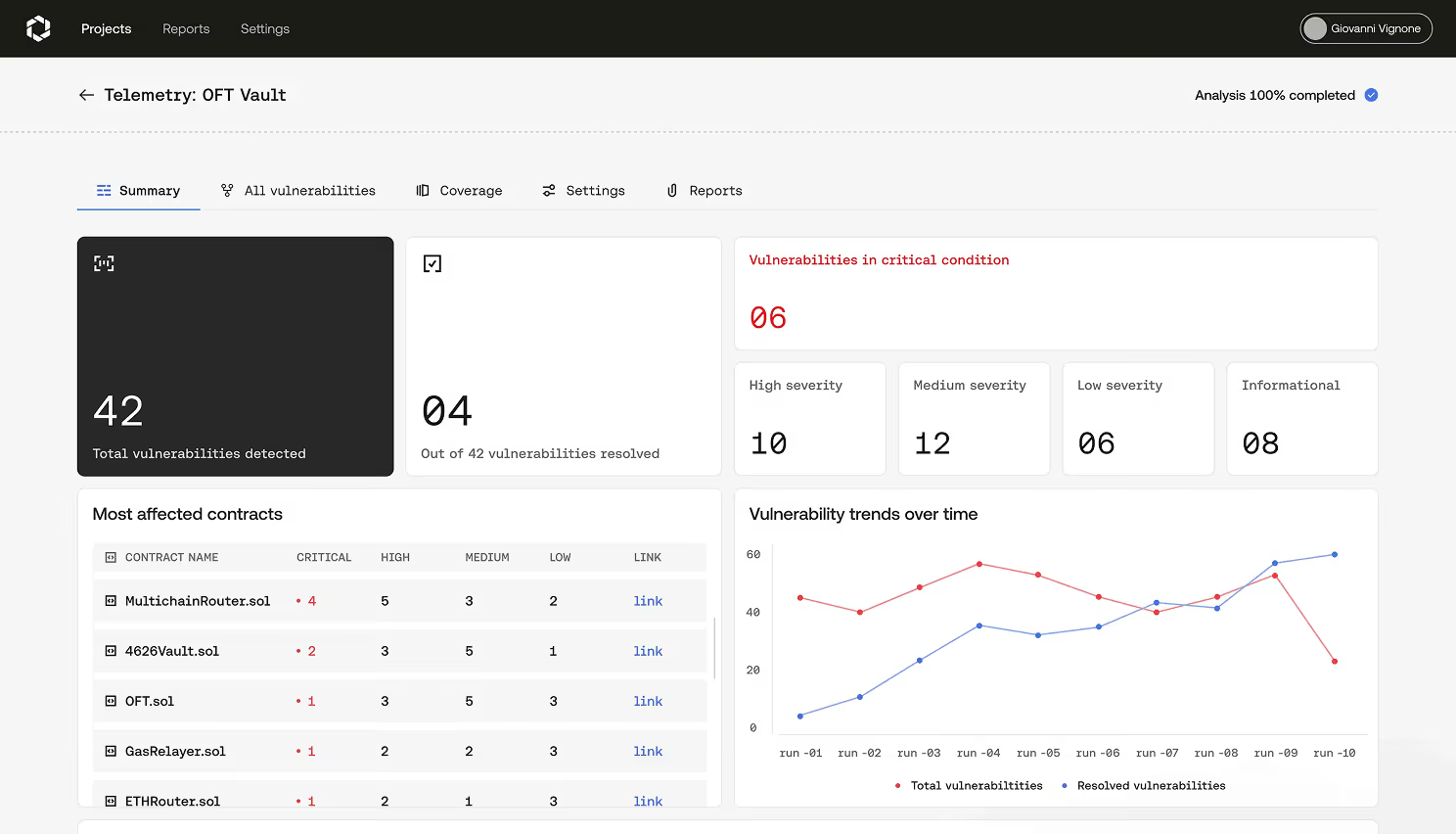
DeFi runs at exploit speed
Octane traces your contract’s state transitions, cross-contract calls, and execution order to surface the exact paths an attacker can exploit.
FAQ
Octane uses domain-specific AI agents purpose-built for security analysis to read code the way a senior auditor would. Octane traces data flow, models attacker behavior, and reasons about how functions interact across the full codebase. Unlike pattern-matching scanners, Octane evaluates business logic and protocol-specific intent, surfacing the kinds of vulnerabilities traditional tools miss because they require reasoning, not just rules.
Octane validates every finding against the full execution context of your codebase rather than the file a flaw appears in. The platform traces whether a suspicious pattern is actually reachable, exploitable, and material — discarding findings that look risky in isolation but are constrained by upstream guards. Engineering teams receive a triaged list of real, exploitable issues instead of a flood of theoretical alerts.
Yes. Every Octane finding includes a traced exploit path showing how the vulnerability would be reached, what an attacker would do to trigger it, and what assets would be at risk. Rather than flagging a line of code, Octane reconstructs the attack sequence end-to-end so engineering teams can prioritize by real impact and reproduce the issue in test before shipping a fix.
Octane secures all mission-critical software from blockchains to browsers.
Octane is fully language agnostic. If you write code in it, Octane can analyze it.
Yes, and it's one of the most common reasons enterprise teams adopt Octane. AI assistants like GitHub Copilot, Cursor, and Claude Code now generate a substantial share of new commits, yet they frequently introduce subtle authentication, input-validation, and access-control flaws. Octane reviews AI-generated code with the same depth as human-written code, providing the continuous security review that AI-assisted development requires to ship safely.
Octane covers Ethereum and all EVM-compatible chains (Arbitrum, Optimism, Base, Polygon, BNB Chain), Solana, Aptos, Sui, and Cosmos-based chains, with additional networks added on a rolling basis. Coverage extends to Layer-2 rollups, cross-chain bridges, and protocol code at the validator and consensus layer – the surfaces where the largest losses have historically been concentrated.
A traditional smart-contract audit is a point-in-time human engagement – typically four to eight weeks long – that ends when the report is delivered. Octane is continuous: it reviews every commit, dependency change, and protocol upgrade with the same depth as a human auditor, but without the four-week latency or six-to-seven-figure per-engagement price tag. Most leading protocols pair Octane with human audits, treating Octane as the layer that catches what's introduced between review cycles.
Octane provides deeper insights than SAST or DAST tools by tracing vulnerabilities through your codebase to show you how they can be exploited. SAST tools rely on pattern-matching against known signatures and flood teams with low-context findings; DAST tools require a running application and miss anything not exposed at runtime. Octane reasons through business logic and full execution paths, surfacing the real, exploitable issues that matter. As such, Octane can replace your need for SAST and DAST tooling.
Halborn, Trail of Bits, OpenZeppelin, and ChainSecurity are human-led audit firms that engage on point-in-time projects. Octane is a continuous AI security platform. Many leading protocols pair the two: a respected human audit at major release milestones, and Octane in the background reviewing every commit, dependency, and upgrade in between. The role of Octane is to ensure the security posture you paid an auditor to certify does not decay between engagements.
Most teams are reviewing live Octane findings within hours, not weeks. Octane connects directly to your code repository, runs initial analysis on the existing codebase, and begins surfacing findings on every subsequent commit. No production access required. Full integration, including CI/CD connection and team onboarding, can be done in less than a day.
Yes. Octane integrates natively with GitHub and GitLab, surfaces findings directly in pull requests, and plugs into CI/CD pipelines. Findings can be configured to block merges, comment on PRs, or feed downstream ticketing — meaning security review becomes part of every developer's existing workflow rather than a separate gate.
.avif)